Toronto Police Arrest Crew Behind First Known SMS Blaster Attack in Canada
Authorities say the operation, which began in November 2025, disrupted emergency 911 services and aimed to steal banking credentials

Toronto police have arrested three men and laid 44 charges against them for allegedly operating an SMS blaster in downtown Toronto since November 2025. Authorities confirm this is the first known instance of an SMS blaster being used in Canada, marking a significant escalation in local cybercrime operations. The crew operated a uniquely built device from the back of a vehicle, allowing them to move across the city while spoofing cell towers to intercept mobile traffic.
The attack exploited security weaknesses in older 2G cellular networks to flood tens of thousands of devices with malicious text messages containing phishing links. Once nearby phones and tablets connected to the blaster's stronger signal, the device broadcast thousands of messages designed to impersonate legitimate businesses. The operation aimed to steal usernames, passwords, and banking credentials, with Detective Sergeant Lindsay Riddell of the Toronto Police Service detailing the intent during a press conference.
Beyond the theft of personal data, the scheme had serious implications for public safety. The police stated that the device disrupted nearby cellular communications and interfered with emergency 911 services. By overwhelming the network with spammy text messages, the crew created a bottleneck that could have prevented citizens from reaching emergency responders during critical moments.
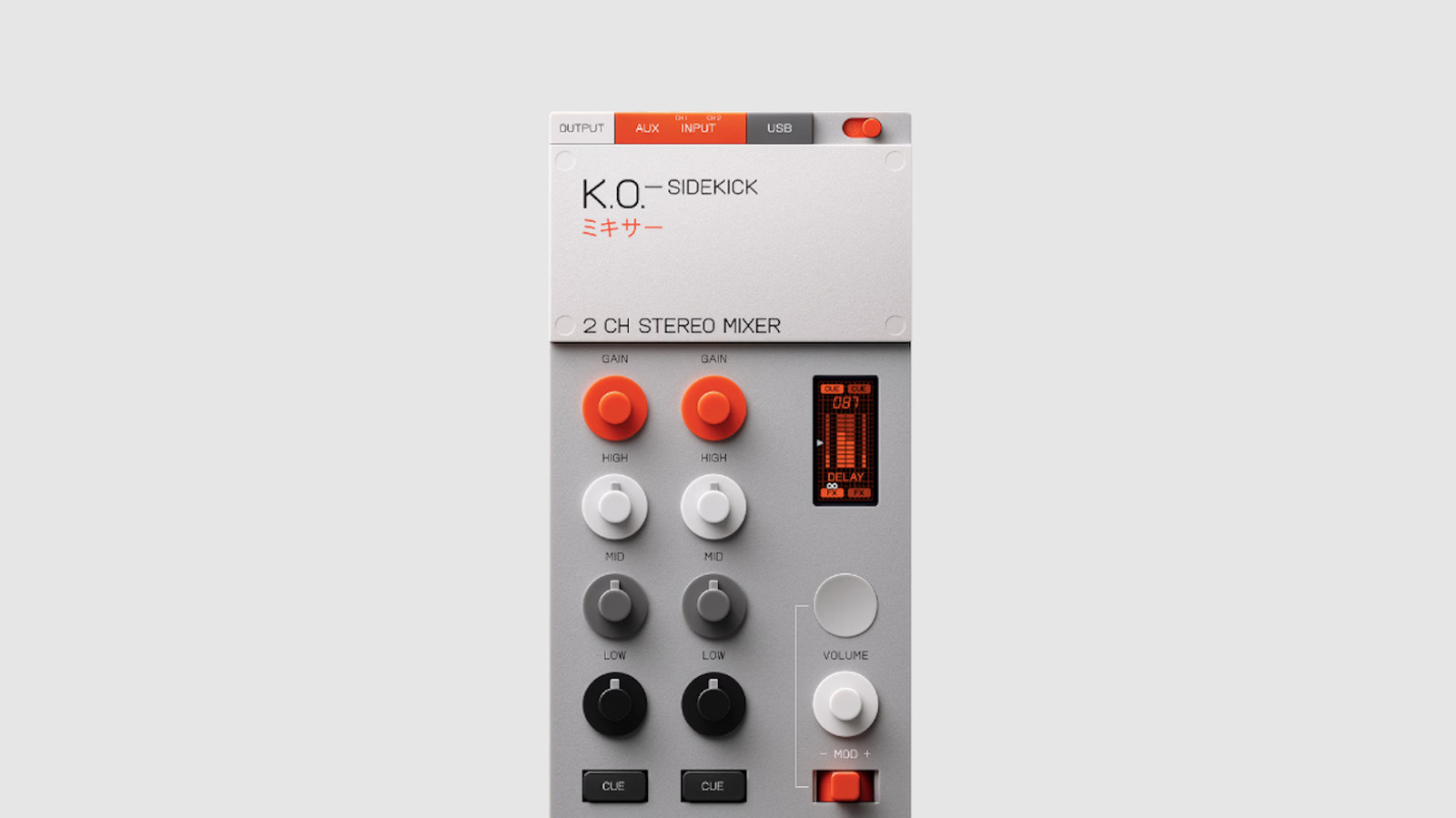
While Toronto authorities declined to share a photo of the seized device citing safety reasons, they released an image of a similar SMS blaster found in the United Kingdom during an earlier investigation. The Toronto device was described as custom-built, distinguishing it from standard equipment and highlighting the sophistication of the group behind the attack.
This case follows a similar international operation in 2024, where Thai police arrested a gang in Bangkok for running an SMS blaster out of a truck. That group reportedly sent close to a million messages in just three days, demonstrating the mobility and potential scale of such cyberattacks. The Toronto investigation underscores that these threats are not isolated to specific regions but represent a growing global risk to mobile infrastructure.
In response to the threat, users are advised to mitigate risk by switching off their phones' 2G cellular connectivity. Users of Apple devices can further protect themselves by enabling Lockdown Mode, which switches off 2G radios. The Toronto Police Service continues to investigate the full extent of the damage, though the exact number of successful credential thefts remains unquantified at this time.